Effective July 2018, the Importance of HTTPS in Chrome
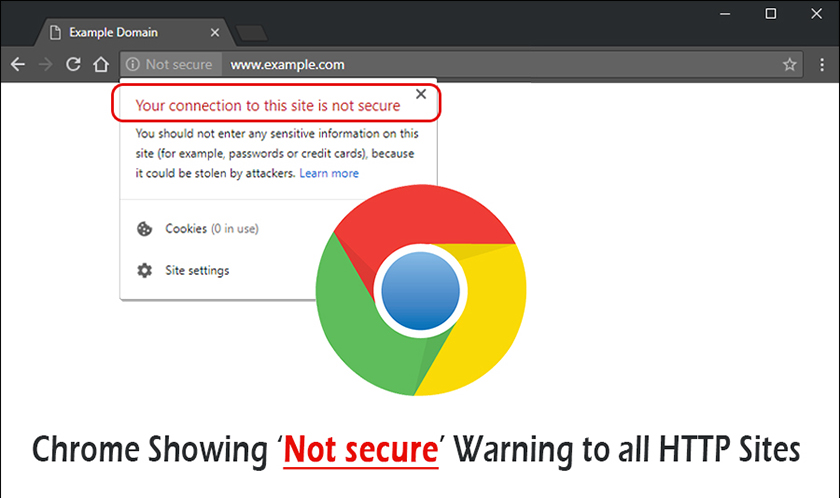
As 2018 forges on, the importance of HTTPS in Chrome picks up steam. After years of pushing for ‘secure by default’ web sites, Google will now identify insecure sites in the Chrome browser beginning mid-Summer.
Designed to ward off ‘man in the middle attacks’, HTTPS protects data while in transit by use of bidirectional encryptions. Over 33% of Alexa’s top 1 million website use HTTPS by default, with 70% of page loads using hypertext transfer protocol secure.
As HTTPS utilizes transport layer SSL technology to permit browsing, buying and gaming to be secure, most browsers have made necessary changes to allow HTTPS to exist naturally. Updated X.509 digital certificates provide adequate security through ports 443 or 80, at least in Firefox, Edge and Safari.
Brief History of HTTPS
First invented by Netscape engineers around ’94, top browsing tool Netscape Navigator received the first dose of HTTP pagination on a secured level. It primarily used SSL technology yet quickly adopted TLS (transport layer security) protocols upon RFC 2818’s standardization of HTTP over TLS back in early 2000.
RFC established precedence on correct implementation of HTTPS both server-side and client-side, and URI’s were the primary target for proper formatting. Today, HTTPS utilizes most all TLS communications over Port 443 and is written into browsers and server software rudimentarily, although SSL technology still assists in keeping the entire browsing experience safeguarded.
Today, HTTPS is a mere formality in the billions of daily requests served between Shanghai and Seattle. But nothing ‘concrete’ by way of security has been rolled out to thwart the usefulness of this secure means of passing data between two points.
HTTPS Should Always Be #1. Even in Chrome.
Aside from your confidentiality and identification, Chrome programmers and website servers should always make reasonable strides to improve the encryption of requests across miles of fiber optic wires. While Firefox and Edge (or Internet Explorer, if you’re old school) have hunkered down on HTTPS, Chrome is starting to lay off – although they shouldn’t.
If you wish to share Twitter or Facebook interactions with unidentified sources, feel free to browse with HTTP only – you’ll probably experience your social interactions being hijacked and spread across other internet sites which only intends on harming your usually good persona.
Here are some compelling reasons you’ll always need to use HTTPS for browsing the internet using Chrome:
- Open Wi-Fi Networks Are Cruel
HTTPS is usually negated, and compromised, when using open networks to access the internet from libraries, restaurants or cybercafés. Hackers will poach unaware web surfers through these open networks and control your every movement – or at least copy it. Therefore, by using only secured networks and appending an SSID as your network identifier, HTTPS will again remain secure regardless of what the bad guys are doing to open network sessions. - Mobile Apps Are Unproven
Remember the Apple contributing developer who purposely exposed iTunes Store vulnerabilities by uploading an unscanned, undetected and pretty normal application for download? This proves that not only are mobile apps not HTTPS secure, they’re prone to virus attacks. If accessing mobile applications means jeopardizing the use of HTTPS, it should be never considered again until mobile browsers can fully comply with secure encryption as they have with IE and Firefox. - Payment Pages Are Susceptible To SQL Injections
Although still denied today, GoDaddy was once victim of SQL injection attacks which knocked millions of websites offline for several hours. The company has since vowed it was ‘networking issues’, the point is still clearly visible: HTTPS is needed to avoid payment page and general datacenter injection attacks which probably could’ve been avoid if proper measures were taken to thwart attacks of this nature. HTTPS is also necessary to culminate with SSL/TLS and TCP/IP security to make the entire website visitation experience tightened down.
Improve Chrome’s HTTPS by Terminating SSL Early
Performance of websites accessed by Chrome will always be under scrutiny, whether that chastisement comes from users or other programmers. Since cross-country HTTPS connections require several handshakes and thereby are imposed 200ms penalties, sending HTTP traffic over to secure connections isn’t always plausible. Therefore, cutting down secure sockets layer connections sometimes is the lesser of security evils which programmers much select.
So, if your business is located in New York and your request is going to Seattle, expect two full trips of authentication to occur unless the below method of HTTPS masking is implemented into your page schemas.
- By implementing load balancers on both ends of browser communication, the requests are sent to home location and recipient, making the initial SSL greeting.
- The greeting would normally return and therefore, after authentication, become secure at the home server hosting the page.
- Using Early SSL termination, the handshake and ensuing SSL drop off are all completed right where the web surfer is located which terminates the extra handshakes.
The improvements of requests, and the elimination of ‘request timeout’ altogether reside in the 65% region simply by implementing this load balancing exchange. It’s tricky and requires some basic coding knowledge of HTTP and TCP/IP protocols yet will drastically cut down on dropped or exposed security.
Chrome engineers are learning this quickly. But, as Chrome 69 takes front stage, it may be too little too late.
Will Chrome Increase HTTPS Security Further?
According to news posted on The Verge, Google Chrome will remove the secure indicator from HTTPS sites this September. Will this change in visual cues destroy the browser’s trustworthiness? The search giant acquiesces.
Eavesdroppers out to sniff ports or swipe packets have been held at bay. Well, for the most part.
Personal blog sites, which normally won’t pass credit card or sensitive personal information between two points, may also benefit from the adoption of HTTPS as Google begins flagging non-HTTPS sites starting in Chrome 68. May seem arbitrary to worry about securing your recipes, but consider this: an SQL injection can wreak havoc in shared hosting environments.
This means attacks meant for a small finance company could wipe out your SQL database inadvertently.
All told, HTTPS has become easy-to-integrate, cheap yet necessary. Chrome must find ways to evolve and keep handshakes between servers secure unless they wish to reinvent the SSL wheel.